SDH Ring Architecture and Switching : In this article, especially will discuss SDH basic ring configuration and features of SNC-P and MS-SPRing (BLSR) Protection methods. Apart from this, we will also try to know how the protection switch architecture of SDH works. In particular, to read about the SDH ring protection and switching system, the entire article has to be read. Just by looking at the topic, the whole thing cannot be understood.
➤SDH Path protection switch (PPS) / Line protection switch (LPS)
➤1+1 protection switch / 1:N (1:1) protection switch
➤Stand-by Line Access (SLA)
➤Unidirectional switch / Bidirectional switch
➤Unidirectional ring / Bi-directional ring
➤Revertive switch / Non-revertive switch
➤Manual switch operation
➤Wait to restore (WTR) time.
It is important to understand above listed items related to protection switching, before proceeding to detailed explanation of ring protection systems.
They are basic and common to not only ring systems but also linear protection systems.
Various combinations between above items are possible, like...
➤(PPS)-(1+1)-(Uni-)-(Non-revertive) this combination is called single ended path switch.
➤(PPS)-(1:1)-(Bi-)-(Revertive)-(SLA) this combination is called dual ended path switch.
➤(LPS)-(1+1)-(Bi-)-(Non-revertive) etc.
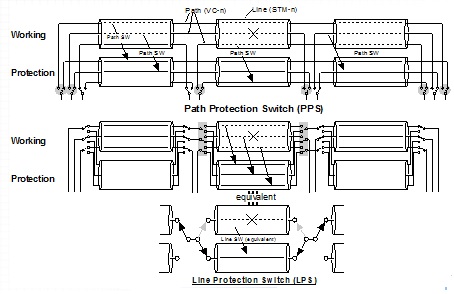
Now I will discuss about each protection switch here. To understand the type of SDH protection switch properly, watch the above image carefully.
Usually 1+1 uses nonrevertive switch and 1:1 and N:1 uses revertive switch, but of course other way round is possible.
In 1:1 or N:1 protection, when the protection line is not occupied by a normal traffic, it can carry a low priority extra traffic. When failure occurs in working line the extra traffic is removed form the protection line and the line is used by the affected normal traffic.
This arrangement is called Stand-by Line Access (SLA). Bidirectional switch is required. Usually a revertive switch is applied for SLA, but for 1:1 non-revertive type SLA is also possible by using slightly complicated configuration.
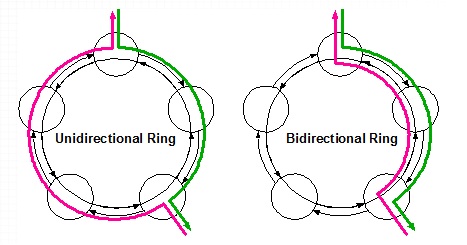
Unidirectional Ring
Normal routing of the traffic is that one direction of two-way connection uses the right (or left) half of the CW (or CCW) line and the other direction uses the left (or right) half of the same CW (or CCW) line. Thus both directions travel around the ring in the same direction and uses capacity (a channel in STM-N) along the entire circumference of the ring.
Total number of connections in the ring cannot exceed the capacity of each section. Unused line (above case CCW) is for protection capacity.
Bidirectional Ring
Normal routing of the traffic is that both directions of two-way connection routed using the same section(s) and node(s). Corresponding channel of the STM-N in unused half (above case left half) can be assigned for other connections which has no overlap section each other.
Total number of connections in the ring can exceed the capacity of each section. Protection capacity is provided by dividing the section capacity half (for 2 fiber ring) or using additional fiber pair (4 fiber ring).
Whenever switching is applied and if a complicated hitless switching is not employed it is inevitable to cause data hit, short period error. To avoid the unnecessary errors this scheme is important, especially in 1+1 protection system. Non-revertive 1:1. SLA is also possible by a different design method.
MSW- Manual Switch
SF- Signal Failure
FSW- Forced Switch
LKOW- Lock Out of Working
LKOP- Lock Out of Protection
For the protection switching system, manual operations, which are listed above, are possible. They are used for maintenance purposes.
The traffic on a selected system is transferred to the protection system by the MSW. When a failure is detected on another system & SF, signal failure & the MSW is released and the failed system takes over the protection system.
The FSW does the same switching as the MSW, but against other system failure it does not release the protection system.
When the LKOW is applied to a working system, it is not switched to the protection system even if it fails. Under this status neither MSW nor FSW can be applied.
The LKOP is practiced to the protection system, any switching to it is refused, either automatic (SF) or manual (MSW and FSW.) Priority order among operations is above order. The larger the number is, the higher the priority. No priority difference between LKOP and LKOW.
In the revertive switching mode, to prevent frequent back-and-forth switching between the working and protection because of intermittent fault, the failed working must be error-free. To ensure this, the wait-to-restore (WTR) time is set.
During WTR period if a fault is detected on the waiting working system, the WTR time is reset.
Ring Configuration provides reliability to the network’s traffic. Traffic is protected because it can flow between any two points in either of two directions in the ring: Clockwise or Counterclockwise.
Rings can be Two Fiber (2F) or Four Fiber (4F). The ring shown above is a 2F Ring (one pair of fibers between adjacent nodes of the ring). Additional reliability can be obtained by the deployment of 4F Rings.
In a 4F-Ring, nodes are interconnected by two pairs of fibers. The main pair is known as the Working Fibers (W), and the second pair is known as the Protection Fibers (P).
There are two basic protection schemes for the Ring Architecture, which will be explained throughout this article.
The SDH Ring systems are classified into five types based on employed switching method combination (unidirectional or bidirectional switch and path or line switch), routing of two-way traffic (unidirectional or bidirectional ring) and fiber number (2 or 4 fibers).
We can assume for a little time that theoretically any combination between switching and routing direction is possible. But in ring systems, the above uni-uni and bi-bi combination are used.
SNCP-ring (Unidirectional)
It is also called 2-fiber Unidirectional Path protection Switch Ring (2F-UPSR)
No switching protocol is required. This is a simple and fast switching scheme.
SNCP-ring (Bidirectional)
2-fiber Bidirectional Path protection Switch Ring (2F-BPSR). In SDH SNCP ring must be controlled at a path level and protocol by K3 or K4 in POH is required. It is not standardized yet by ITU-T.
4F MS-SP ring
4-fiber Bidirectional Line protection Switch Ring (4F-BLSR). Protocol by K1 and K2 in MSOH is required.
2F MS-SP ring
2-fiber Bidirectional Line protection Switch Ring (2F-BLSR). Protocol by K1 and K2 in MSOH is required.
The 4 / 2F MS-SP ring has two different algorithms, terrestrial applications and transoceanic applications.
SNCP-unidirectional ring (2F-UPSR) uses 2 fiber unidirectional ring architecture and Unidirectional 1+1path switch scheme.
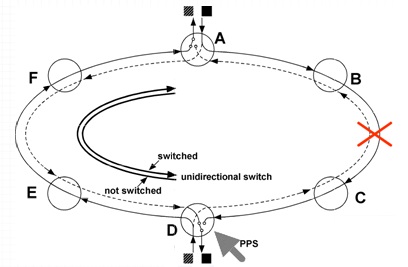
The drawing shows a 2-way connection (A-D, as an example) which uses a channel (time slot) in the STM-N signal. The solid line indicates the channel in the clockwise (CW) STM-N (fiber) and the broken line the corresponding channel in the counter clockwise (CCW) STM-N. Other connections between any other nodes are made by using different channels of the STM-N.
At the transmitting node (A) the traffic is branched onto both CW and CCW STM-N and at the receiving node (D) one of them carried by CW and CCW is selected by a path protection switch (PPS). Opposite direction (D to A) is arranged in the same way using the same channel on the unused semicircle.
Under the normal status, PPSs at A and D select CW signals, making a unidirectional ring. The signals on CCW are stand-by signals.
It is possible to set the one of the PPS to CCW. In this case both direction traffic travel on the same route. This makes transmission delay of both directions equal. This is a bidirectional-like setting but the system is still SNCP-unidirectional ring.
An important point of the system is that one path occupies one channel of the STM-N (both CW and CCW) along the entire circumference of the ring. As a result, total number of paths in a ring cannot exceeds STM-N’s capacity.
There is no limitation to the node number in an SNCP-ring from the point of view of the ring control, but the STM-N capacity determines the limit. Operators can selectively provision paths to be protected or unprotected. Unprotected path will only use capacity in the selected route (semicircle). The other route will provide additional unprotected path(s).
Under the (line and path) failure status-
When failure or degradation is detected on the currently selected signal, the switch position of the PPS is changed (above case, CW to CCW at D node.) Unaffected direction of the path does not activate the PPS (above case, at A.)
The activation of the PPS does not require protocol between nodes. Failure detection and PPS activation are done by the receiving node alone. This makes system control simple and as a result, the switching time short.
When the failure is at the line (STM-N) level, all (or many) paths in the ring are suffered and PPS switching occur independently at every concerned nodes.
For the bidirectional-like setting, when the failure is at the line level, both directions are switched at the same time. But they are considered as independent unidirectional switching.
This cause data hits to both directions. But for normal unidirectional ring arrangement, the data hits are only on one direction.
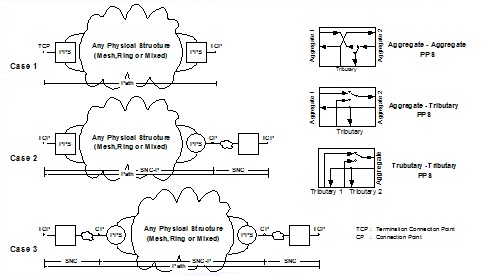
General SNCP has wider definition than previously explained SNCP-ring. The SNCP-ring is a one type of the SNCP.
The SNCP can have any type of network physical structure (i.e. meshed, ring or mixed) between PPSs. The SNCP-ring (2F-UPSR) is limited to the ring configuration.
A path can be subdivided to subnetwork connections (SNC) as described above. The CP is a connection point of SNCs. The TCP is a path termination point.
The SNCP can be used to protect a portion of a path (e.i. a SNC), by setting PPSs at two CPs (Case 3) or at a CP and a TCP (Case 2) or the full end-to-end path putting PPSs at two TCPs (Case 1).
To make the SNCP flexible, three types of PPS should be available. They are Aggregate-Aggregate PPS, Aggregate-Tributary PPS and Tributary-Tributary PPS. Implementation of all or some of them to equipment depends on its design. The SNCP-ring (2F-UPSR) uses only Aggregate-Aggregate PPS.
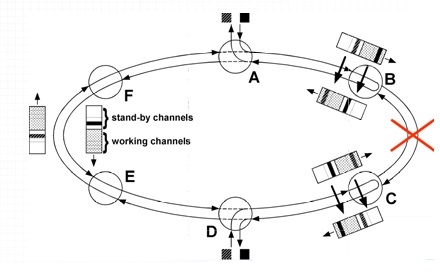
4 fiber MS-SP ring (4F-BLSR) uses 4 fiber bidirectional ring architecture and Bidirectional 1:1 line switch scheme. A pair of fiber is for the working line and the other for the protection line.
The solid and broken lines show the same channels (time slots) in the working and protection STM-Ns respectively. Different from the SNCP-ring, both directions of a 2-way path are directed to the same route and they are not branched onto the protection channel.
The corresponding channel on the second semicircle (left, in the drawing) is vacant, so it is possible to arrange other paths, like another A-D or D-E and E-A, etc., by using the same channel. Of course those paths must not have overlaps. The overlapped paths must use different channel of the STM-N. As a result, total number of paths in the ring can exceed the STM-N capacity.
The SLA (Stand-by Line Access) is possible. It requires the switching protocol carried by K1 and K2 of MSOH. The maximum number of nodes is limited to sixteen (16). This is determined by the control protocol (standard). Four bits in K1 are assigned to indicate the message destinations, resulting in maximum 16 nodes.
Against a total section failure (both working and protection), the traffic on the working fiber is looped to the corresponding channel of the opposite direction protection fiber at the both ends of the failed section (B and C).
The looped traffic passes through both originating and destination nodes and looped back to the working fiber at the other end of the failed section (C and B).
The same applies to all other channels which are used by other path, i.e. the loop at B and C and the through at other nodes. The result is just as if the traffic is looped at the STM-N level or the fiber. That is why this system is categorized to the line switch.
The line switch takes place at the failed section side of the node. That is, at C node it is not at the side facing D node but at the side facing B node.
Now the long route (C-D-E-F-A-B) is used as a protection line for the short rout (B-C). In this way, the protection ring is shared by all sections (MS) in the ring.
This switching against a total section failure is named “Ring Switch .”
Unaffected paths, e.g. paths between C-D,E-A etc., remain on the working fiber.
Against multiple section failure, all of paths cannot survive, some of them are killed. When a node failure occurs, e.g. at C node, ring switches take place at B node and D node. They are at the sides facing C node.
2 fiber MS-SP ring (2F-BLSR) uses 2 fiber bidirectional ring architecture and
Bidirectional 1:1 line switch scheme.
To provide protection channels, the STM-N capacity is divided into two parts. The first half is assigned to the working channels and the second half is for the protection. The path arrangement is same as the 4 fiber MS-SP ring including reuse of channels.
The total maximum number of paths in the ring is half of 4 fiber MS-SP ring, under the same conditions.
The SLA is possible. Same protocol as 4 fiber ring is used and the maximum node number is also sixteen (16).
Against a section failure, the loop switching takes place at both end of the failed section (B and C). The traffic carried by a channel of the working half of STM-N is transferred to the corresponding channel of the protection half of opposite direction STM-N.
It travels the long route passing originating, destination and other nodes (A, F, E and D). At the remote end it is switched back to the working half of the opposite direction (original fiber).
There is no Span Switch for 2 fiber ring. Unlike 4F MS-SP, no survivability against multiple failures. Other points are same as 4 fiber ring.
In the protocol exchange, the node ID is used to indicate a message destination.
The cross connection table of each node must be provided with information that shows the originating and destination node of each path indicated by the node ID.
Each node must have knowledge of the IDs assigned to all other node in the ring and their sequence. The node ID map, which is provisioned to each node, provides this information. When nodes are added to the ring, the node ID map must be revised.
When C node fails ring switches take place at B and D nodes. B node does it to save A-C path and D node to save C-F path. And they are switched to the same protection channel.
The result is that previous two independent paths are changed to single A-F connection. This is inevitable and the system send out an AIS (Alarm Indication Signal) to the misconnection paths in order to avoid inconvenience.
If the MS-SP ring has sections with very long length, e.g. a transoceanic submarine cable, and the ring switch is applied like a terrestrial system, the traffic must cross a ocean back and forth under failure condition, resulting in very long delay. To solve the problem different algorithm called the transoceanic application is standardized (also in G.841).
In this algorithm, instead of the ring switch, the affected path is switched to the corresponding channel of the protection capacity of opposite direction at the path terminating node. The same occurs at all nodes that have suffered paths. Actually, this is not a line switch but a path switch. The result is same as the SNCP bidirectional ring but the protocol does not use K3 or K1 of POH and algorithm is different.
When a section failure occurs, B and C exchange protocol via the protection fiber of the long route (B-A-F-D-E-C) using K1 and K2. Nodes A, F, E and D can monitor the exchange, decide which of their paths are in trouble and take the above action at the path level. For this protocol the DCCr is also used to exchange the path mapping information.
Against the on-only-working type failure on 4F MS-SP, the span switch(s) are applied in the same way as the terrestrial system.
When a path is laid over two rings, it can survive against a ring failure by the self-healing function of the ring. But the failure is on the link that connects two rings, it will be killed.
By connecting two rings by two links and diverting the traffic to the second link against the first link failure, the survivability of the path can be improved. This method is named Inter Locked Ring (ILR).
The ILR is possible for any combination of two rings, MS-AP~MS-AP or SNCP~SNCP or MS-SP~SNCP.
Two nodes where the links are connected are named the primary node and the secondary node. The two nodes are not necessarily neighbor nodes. It is possible to put nodes between the primary and the secondary. The ILR setting is on the path bases. It is not necessary to set ILR to all of paths that pass the link.
There are two types of MS-SP ~ MS-SP ILR depending on whether the working capacity or the protection capacity connects the primary and the secondary node. This drawing shows on-working case.
MS-SP~ MS-SP ILR (P-S on-working): At the transmitting side primary node the traffic is branched on to the first and second link routes. At the receiving side primary node a service selector (SS) is installed and it choose a normal signal carried by the first or the second link. Either failure on the first or the second link can be protected. The path connections between four node (two primaries and two secondary nodes) is same as the SNCP. The SS works as the PPS.
The right side drawing explains the protection against a section failure on the ring. Usual ring switch or span switch (not shown) takes place. Thus a double failure on the link and the ring can be protected.
The connection between the primary and the secondary nodes uses the working capacity. A demerit of this configuration is that it consumes a part of the working capacity for protection purpose and reduces efficiency of the ring.
MS-SP ~ MS-SP ILR (P-S on-protection):
Connection between the primary and the secondary uses protection capacity. The switching against the link failure is quite same as previous one. One against the ring failure is completely different and complicated.
Against the ring failure, the same ring switches take place at the failed section. The traffic is looped to the protection capacity but when it reaches to the primary node it has no way to go further, because a part of the protection capacity is occupied by the ILR.
To vacate the protection capacity to the ring-switched traffic, automatic reconfiguration of the ILR is carried out at the primary and the secondary. The SS and the branching for the opposite direction at the primary is transferred to the secondary as shown in the drawing. And the traffic on the first link is directly connected to the working capacity of the ring. Now the ILR is ready for a failure on the links. This is named “SS transfer.”
The merit of this configuration with complicated ring control is it does not consume any of the working capacity of the MS-SP ring. The same total ring capacity as an independent MS-SP can be realized.
On the SNCP ring, the input traffic from a link ( tributary ) line is transmitted to only one direction, the first link to CCW and the second link to CW.
Therefore, depending on the mode of double failure on the ring and link, there is a case where the path cannot be protected. Above drawing explain the protected and unprotected situations. The MS-SP ring does not have this inconvenience.
It is important to understand about SDH related to protection switching, before proceeding to detailed explanation of ring protection systems. They are basic and common to not only ring systems but also linear protection systems. Below are some specific points that have to be read carefully.
SDH Basics Protection Switch Architecture
Some important protection and switching system of SDH mentioned as -➤SDH Path protection switch (PPS) / Line protection switch (LPS)
➤1+1 protection switch / 1:N (1:1) protection switch
➤Stand-by Line Access (SLA)
➤Unidirectional switch / Bidirectional switch
➤Unidirectional ring / Bi-directional ring
➤Revertive switch / Non-revertive switch
➤Manual switch operation
➤Wait to restore (WTR) time.
They are basic and common to not only ring systems but also linear protection systems.
Various combinations between above items are possible, like...
➤(PPS)-(1+1)-(Uni-)-(Non-revertive) this combination is called single ended path switch.
➤(PPS)-(1:1)-(Bi-)-(Revertive)-(SLA) this combination is called dual ended path switch.
➤(LPS)-(1+1)-(Bi-)-(Non-revertive) etc.
Path protection switch Line protection switch
In above drawing, a thin line shows a path (VC-n or channel in STM-N) and a pipe means a line (STM-N signal or multiplex section).
Path Protection Switch
Protection switches are set up at the ends of each path. Against a line failure, protection switching take place at the ends of suffered paths. Against a failure in a single path, switching is applied only to the path. Usually path performance monitoring initiates the switching. A line failure results in a path failure and the path failure detection causes switching, not the line failure detection.Line Protection Switch
Switches are set individually to all channels of the STM-N at both ends of a section. Against a line failure, all channels are switched to corresponding channels of the protection line. Although the switching is at a channel (path) level, it is equivalent to that the line (fiber) is switched. The switching is triggered by the section failure detection. Failure detection in a path does not cause the line switching.1+1, 1:1 and 1:N Protection Switch
 |
| SDH protection switch |
1+1 Protection Switch
At the transmitting side the normal signal (traffic) is permanently branched onto both working and protection lines. Against failure on the working switching takes place at the receiving side only. This switching scheme does not require switching protocol.1:1 Protection Switch
Switches are installed at both transmitting and receiving side. This structure requires switching protocol. Under normal condition, the protection line carries an idle signal or a low priority extra traffic which will be removed when the working fails.N:1 Protection Switch
In this scheme one protection line is provided for N working lines. Switching protocol is necessary and the protection line can carry an extra traffic while it is not used by one of normal traffics.Usually 1+1 uses nonrevertive switch and 1:1 and N:1 uses revertive switch, but of course other way round is possible.
Stand-by Line Access (SLA)
 |
| Stand-by Line Access (SLA) |
This arrangement is called Stand-by Line Access (SLA). Bidirectional switch is required. Usually a revertive switch is applied for SLA, but for 1:1 non-revertive type SLA is also possible by using slightly complicated configuration.
Unidirectional Switch and Bidirectional Switch
 |
| SDH unidirectional and bidirectional switch |
Unidirectional Protection Switch
When the failure is only on one direction, only the affected direction traffic is transferred to the protection line. For 1+1 system, this is a simple method because no protocol is necessary and switching can be determined only at a receiving side. Disadvantage is that under protection status different directions use different hardware and line and they might have different propagation time.Bidirectional Protection Switch
Even if a failure is only on one direction, both affected and unaffected directions are switched to the protection line. This switching scheme requires a protocol, because the unaffected direction receiver has no way to detect the failure until it is informed by the remote side. Both directions of transmission maintain equal delays and this may be important where there is a significant length imbalance for the working and protection.Unidirectional Ring and Bidirectional Ring
 |
| Traffic routing under normal |
Normal routing of the traffic is that one direction of two-way connection uses the right (or left) half of the CW (or CCW) line and the other direction uses the left (or right) half of the same CW (or CCW) line. Thus both directions travel around the ring in the same direction and uses capacity (a channel in STM-N) along the entire circumference of the ring.
Total number of connections in the ring cannot exceed the capacity of each section. Unused line (above case CCW) is for protection capacity.
Bidirectional Ring
Normal routing of the traffic is that both directions of two-way connection routed using the same section(s) and node(s). Corresponding channel of the STM-N in unused half (above case left half) can be assigned for other connections which has no overlap section each other.
Total number of connections in the ring can exceed the capacity of each section. Protection capacity is provided by dividing the section capacity half (for 2 fiber ring) or using additional fiber pair (4 fiber ring).
Revertive Switch and Non-reverteve Switch
 |
| Revertive and Non reverteve Switch in SDH system |
Rivertive Switch
When the failure in the working system is repaired, the traffic that has been carried by the protection system is switched back to the working system. When the SLA is employed, usually this switching scheme is used and also in N:1 system to vacate the protection system for the next failure.Non-revertive Switch
After the recovery of the failed working system, the traffic is not switched back to the working system. When the protection system fails later, traffic is transferred to the working. Therefore it is not appropriate to name “working” and “protection” and often they are called “0” and “1” system.Whenever switching is applied and if a complicated hitless switching is not employed it is inevitable to cause data hit, short period error. To avoid the unnecessary errors this scheme is important, especially in 1+1 protection system. Non-revertive 1:1. SLA is also possible by a different design method.
Manual Switch Operation
Some types of manual switching are given below-MSW- Manual Switch
SF- Signal Failure
FSW- Forced Switch
LKOW- Lock Out of Working
LKOP- Lock Out of Protection
The traffic on a selected system is transferred to the protection system by the MSW. When a failure is detected on another system & SF, signal failure & the MSW is released and the failed system takes over the protection system.
The FSW does the same switching as the MSW, but against other system failure it does not release the protection system.
When the LKOW is applied to a working system, it is not switched to the protection system even if it fails. Under this status neither MSW nor FSW can be applied.
The LKOP is practiced to the protection system, any switching to it is refused, either automatic (SF) or manual (MSW and FSW.) Priority order among operations is above order. The larger the number is, the higher the priority. No priority difference between LKOP and LKOW.
Hold-Off & Wait to Restore (WTR) times
 |
| WTR in SDH system |
It is on the order of 5-12 minutes with 1-second increment. To prevent chattering of the protection switch due to an intermittent failure, the working channel must be fault free for a fixed of time before the switch taken to transfer to protection.
During WTR period if a fault is detected on the waiting working system, the WTR time is reset.
Ring Architecture
 |
| Ring Architecture system |
Rings can be Two Fiber (2F) or Four Fiber (4F). The ring shown above is a 2F Ring (one pair of fibers between adjacent nodes of the ring). Additional reliability can be obtained by the deployment of 4F Rings.
In a 4F-Ring, nodes are interconnected by two pairs of fibers. The main pair is known as the Working Fibers (W), and the second pair is known as the Protection Fibers (P).
There are two basic protection schemes for the Ring Architecture, which will be explained throughout this article.
Types of Ring System
There are two basic protection schemes for the Ring Architecture for the ease which is shown by the image below. |
| SDH Types of Ring System |
The SDH Ring systems are classified into five types based on employed switching method combination (unidirectional or bidirectional switch and path or line switch), routing of two-way traffic (unidirectional or bidirectional ring) and fiber number (2 or 4 fibers).
We can assume for a little time that theoretically any combination between switching and routing direction is possible. But in ring systems, the above uni-uni and bi-bi combination are used.
SNCP-ring (Unidirectional)
It is also called 2-fiber Unidirectional Path protection Switch Ring (2F-UPSR)
No switching protocol is required. This is a simple and fast switching scheme.
MS Dedicated Protection Ring2-fiber Unidirectional Line protection Switch Ring (2F-ULSR). In MSOH is required Protocol K1 , K2 and it is not standardized yet by ITU-T.
SNCP-ring (Bidirectional)
2-fiber Bidirectional Path protection Switch Ring (2F-BPSR). In SDH SNCP ring must be controlled at a path level and protocol by K3 or K4 in POH is required. It is not standardized yet by ITU-T.
4F MS-SP ring
4-fiber Bidirectional Line protection Switch Ring (4F-BLSR). Protocol by K1 and K2 in MSOH is required.
2F MS-SP ring
2-fiber Bidirectional Line protection Switch Ring (2F-BLSR). Protocol by K1 and K2 in MSOH is required.
The 4 / 2F MS-SP ring has two different algorithms, terrestrial applications and transoceanic applications.
SNCP (Unidirectional Ring) / 2F-UPSR (1)
 |
| SNCP(Unidirectional Ring) / 2F-UPSR |
The drawing shows a 2-way connection (A-D, as an example) which uses a channel (time slot) in the STM-N signal. The solid line indicates the channel in the clockwise (CW) STM-N (fiber) and the broken line the corresponding channel in the counter clockwise (CCW) STM-N. Other connections between any other nodes are made by using different channels of the STM-N.
At the transmitting node (A) the traffic is branched onto both CW and CCW STM-N and at the receiving node (D) one of them carried by CW and CCW is selected by a path protection switch (PPS). Opposite direction (D to A) is arranged in the same way using the same channel on the unused semicircle.
Under the normal status, PPSs at A and D select CW signals, making a unidirectional ring. The signals on CCW are stand-by signals.
It is possible to set the one of the PPS to CCW. In this case both direction traffic travel on the same route. This makes transmission delay of both directions equal. This is a bidirectional-like setting but the system is still SNCP-unidirectional ring.
An important point of the system is that one path occupies one channel of the STM-N (both CW and CCW) along the entire circumference of the ring. As a result, total number of paths in a ring cannot exceeds STM-N’s capacity.
There is no limitation to the node number in an SNCP-ring from the point of view of the ring control, but the STM-N capacity determines the limit. Operators can selectively provision paths to be protected or unprotected. Unprotected path will only use capacity in the selected route (semicircle). The other route will provide additional unprotected path(s).
SNCP(Unidirectional Ring) / 2F-UPSR (2)
 |
| 2F-UPSR (2) |
When failure or degradation is detected on the currently selected signal, the switch position of the PPS is changed (above case, CW to CCW at D node.) Unaffected direction of the path does not activate the PPS (above case, at A.)
The activation of the PPS does not require protocol between nodes. Failure detection and PPS activation are done by the receiving node alone. This makes system control simple and as a result, the switching time short.
When the failure is at the line (STM-N) level, all (or many) paths in the ring are suffered and PPS switching occur independently at every concerned nodes.
For the bidirectional-like setting, when the failure is at the line level, both directions are switched at the same time. But they are considered as independent unidirectional switching.
This cause data hits to both directions. But for normal unidirectional ring arrangement, the data hits are only on one direction.
Subnetwork Connection Protection (SNCP)
 |
| Sub-network Connection Protection (SNCP) |
General SNCP has wider definition than previously explained SNCP-ring. The SNCP-ring is a one type of the SNCP.
The SNCP can have any type of network physical structure (i.e. meshed, ring or mixed) between PPSs. The SNCP-ring (2F-UPSR) is limited to the ring configuration.
A path can be subdivided to subnetwork connections (SNC) as described above. The CP is a connection point of SNCs. The TCP is a path termination point.
The SNCP can be used to protect a portion of a path (e.i. a SNC), by setting PPSs at two CPs (Case 3) or at a CP and a TCP (Case 2) or the full end-to-end path putting PPSs at two TCPs (Case 1).
To make the SNCP flexible, three types of PPS should be available. They are Aggregate-Aggregate PPS, Aggregate-Tributary PPS and Tributary-Tributary PPS. Implementation of all or some of them to equipment depends on its design. The SNCP-ring (2F-UPSR) uses only Aggregate-Aggregate PPS.
4 Fiber MS-SP Ring / 4F-BLSR (1)
 |
| 4 Fiber MS-SP Ring / 4F-BLSR (1) |
The solid and broken lines show the same channels (time slots) in the working and protection STM-Ns respectively. Different from the SNCP-ring, both directions of a 2-way path are directed to the same route and they are not branched onto the protection channel.
The corresponding channel on the second semicircle (left, in the drawing) is vacant, so it is possible to arrange other paths, like another A-D or D-E and E-A, etc., by using the same channel. Of course those paths must not have overlaps. The overlapped paths must use different channel of the STM-N. As a result, total number of paths in the ring can exceed the STM-N capacity.
The SLA (Stand-by Line Access) is possible. It requires the switching protocol carried by K1 and K2 of MSOH. The maximum number of nodes is limited to sixteen (16). This is determined by the control protocol (standard). Four bits in K1 are assigned to indicate the message destinations, resulting in maximum 16 nodes.
4 Fiber MS-SP Ring / 4F-BLSR (2)
 |
| 4 Fiber MS-SP Ring / 4F-BLSR (2) |
The looped traffic passes through both originating and destination nodes and looped back to the working fiber at the other end of the failed section (C and B).
The same applies to all other channels which are used by other path, i.e. the loop at B and C and the through at other nodes. The result is just as if the traffic is looped at the STM-N level or the fiber. That is why this system is categorized to the line switch.
The line switch takes place at the failed section side of the node. That is, at C node it is not at the side facing D node but at the side facing B node.
Now the long route (C-D-E-F-A-B) is used as a protection line for the short rout (B-C). In this way, the protection ring is shared by all sections (MS) in the ring.
This switching against a total section failure is named “Ring Switch .”
Unaffected paths, e.g. paths between C-D,E-A etc., remain on the working fiber.
Against multiple section failure, all of paths cannot survive, some of them are killed. When a node failure occurs, e.g. at C node, ring switches take place at B node and D node. They are at the sides facing C node.
4 Fiber MS-SP Ring / 4F-BLSR (3)
 |
| 4 Fiber MS-SP Ring / 4F-BLSR (3) |
Against a section failure on the working line only, all traffics carried by the failed section are transferred to the protection fiber of the same section. This switching is named “Span Switch”.
When multiple section failures occur and if they are all working-line-only type failures, the span switches are applied to all of them. And all normal traffics are protected. The 4F MS-SP ring can protect multiple failures of a certain type.
This means network operators can expect 4F MS-SP higher survivability than 2F MS-SP in addition to higher capacity. (cf. 2F MS-SP explanations).
Extra traffics by the SLA that pass through the failed section will be removed.
The system automatically select the ring switch or the span switch depending on the failure mode. Maintenance crews do not have to intervene.
Both in the ring and span switching mode, all traffics are switched to the protection. Unlike SNCP ring, it is impossible to set protected paths selectively. Always all paths in the MS-SP ring are protected.
When multiple section failures occur and if they are all working-line-only type failures, the span switches are applied to all of them. And all normal traffics are protected. The 4F MS-SP ring can protect multiple failures of a certain type.
This means network operators can expect 4F MS-SP higher survivability than 2F MS-SP in addition to higher capacity. (cf. 2F MS-SP explanations).
Extra traffics by the SLA that pass through the failed section will be removed.
The system automatically select the ring switch or the span switch depending on the failure mode. Maintenance crews do not have to intervene.
Both in the ring and span switching mode, all traffics are switched to the protection. Unlike SNCP ring, it is impossible to set protected paths selectively. Always all paths in the MS-SP ring are protected.
2 Fiber MS-SPRing / 2F-BLSR (1)
 |
| 2 Fiber MS-SPRing / 2F-BLSR |
Bidirectional 1:1 line switch scheme.
To provide protection channels, the STM-N capacity is divided into two parts. The first half is assigned to the working channels and the second half is for the protection. The path arrangement is same as the 4 fiber MS-SP ring including reuse of channels.
The total maximum number of paths in the ring is half of 4 fiber MS-SP ring, under the same conditions.
The SLA is possible. Same protocol as 4 fiber ring is used and the maximum node number is also sixteen (16).
2 Fiber MS-SP Ring / 2F-BLSR (2)
 |
| 2 Fiber MS-SPRing / 2F-BLSR (2) |
It travels the long route passing originating, destination and other nodes (A, F, E and D). At the remote end it is switched back to the working half of the opposite direction (original fiber).
There is no Span Switch for 2 fiber ring. Unlike 4F MS-SP, no survivability against multiple failures. Other points are same as 4 fiber ring.
Node ID Map of 4F/2F MS-SP Ring
Each node on the MS-SP ring must be assigned an ID that is a number between 0 and 15. The ID assignment is not necessarily in order. The SNCP ring does not require them.In the protocol exchange, the node ID is used to indicate a message destination.
The cross connection table of each node must be provided with information that shows the originating and destination node of each path indicated by the node ID.
Each node must have knowledge of the IDs assigned to all other node in the ring and their sequence. The node ID map, which is provisioned to each node, provides this information. When nodes are added to the ring, the node ID map must be revised.
MS-SP Ring Misconnection
The 4F/2F MS-SP ring has possibility of making a misconnection when a node fails. |
| Misconnection in ring |
Misconnection
Two paths, A-C and C-F, are terminated at the failed node (C) and they use a same channel of the STM-N. In this case, their stand-by channel in the protection capacity is the same one.When C node fails ring switches take place at B and D nodes. B node does it to save A-C path and D node to save C-F path. And they are switched to the same protection channel.
The result is that previous two independent paths are changed to single A-F connection. This is inevitable and the system send out an AIS (Alarm Indication Signal) to the misconnection paths in order to avoid inconvenience.
No misconnection
When two paths that use the same channel of the STM-N are not terminated at the failed node (through connection), A-E and E-F, the misconnection does not occur. No AIS is sent out to those paths.4/2 Fiber MS-SPRing / 4/2F-BLSR
 |
| 4/2 Fiber MS-SPRing / 4/2F-BLSR |
In this algorithm, instead of the ring switch, the affected path is switched to the corresponding channel of the protection capacity of opposite direction at the path terminating node. The same occurs at all nodes that have suffered paths. Actually, this is not a line switch but a path switch. The result is same as the SNCP bidirectional ring but the protocol does not use K3 or K1 of POH and algorithm is different.
When a section failure occurs, B and C exchange protocol via the protection fiber of the long route (B-A-F-D-E-C) using K1 and K2. Nodes A, F, E and D can monitor the exchange, decide which of their paths are in trouble and take the above action at the path level. For this protocol the DCCr is also used to exchange the path mapping information.
Against the on-only-working type failure on 4F MS-SP, the span switch(s) are applied in the same way as the terrestrial system.
Inter Locked Ring (ILR)
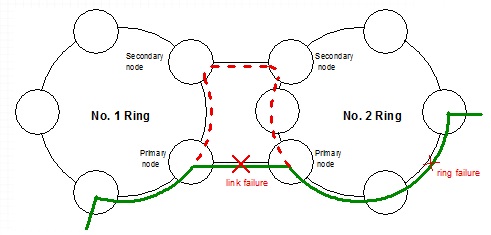 |
| SDH ILR |
By connecting two rings by two links and diverting the traffic to the second link against the first link failure, the survivability of the path can be improved. This method is named Inter Locked Ring (ILR).
The ILR is possible for any combination of two rings, MS-AP~MS-AP or SNCP~SNCP or MS-SP~SNCP.
There are two types of MS-SP ~ MS-SP ILR depending on whether the working capacity or the protection capacity connects the primary and the secondary node. This drawing shows on-working case.
MS-SP~ MS-SP ILR (P-S on-working): At the transmitting side primary node the traffic is branched on to the first and second link routes. At the receiving side primary node a service selector (SS) is installed and it choose a normal signal carried by the first or the second link. Either failure on the first or the second link can be protected. The path connections between four node (two primaries and two secondary nodes) is same as the SNCP. The SS works as the PPS.
The right side drawing explains the protection against a section failure on the ring. Usual ring switch or span switch (not shown) takes place. Thus a double failure on the link and the ring can be protected.
The connection between the primary and the secondary nodes uses the working capacity. A demerit of this configuration is that it consumes a part of the working capacity for protection purpose and reduces efficiency of the ring.
Connection between the primary and the secondary uses protection capacity. The switching against the link failure is quite same as previous one. One against the ring failure is completely different and complicated.
Against the ring failure, the same ring switches take place at the failed section. The traffic is looped to the protection capacity but when it reaches to the primary node it has no way to go further, because a part of the protection capacity is occupied by the ILR.
To vacate the protection capacity to the ring-switched traffic, automatic reconfiguration of the ILR is carried out at the primary and the secondary. The SS and the branching for the opposite direction at the primary is transferred to the secondary as shown in the drawing. And the traffic on the first link is directly connected to the working capacity of the ring. Now the ILR is ready for a failure on the links. This is named “SS transfer.”
The merit of this configuration with complicated ring control is it does not consume any of the working capacity of the MS-SP ring. The same total ring capacity as an independent MS-SP can be realized.
Double Failure on Link and Ring (SNCP/ILR)
 |
| Double Failure on Link and Ring (SNCP/ILR) |
Therefore, depending on the mode of double failure on the ring and link, there is a case where the path cannot be protected. Above drawing explain the protected and unprotected situations. The MS-SP ring does not have this inconvenience.





20 Comments
Dearest friends, thanks for the submission. If you need any changes in it, try this well-reseacrhed piece available at http://findwritingservice.com/blog/the-secret-of-losing-weight-fast-and-its-consequences. You will be satisfied with the post.
ReplyDeleteThis is quite charming post you shared, I like the post, an obligation of appreciation is all together for sharing..
ReplyDeletehttps://360digitmg.com/course/certification-program-in-data-science
There is plainly a ton to consider this. Keep working, remarkable work!
ReplyDeleteiot training in delhi
Incredibly conventional blog and articles. I am realy very happy to visit your blog. Directly I am found which I truly need. Thankful to you and keeping it together for your new post.
ReplyDeletePMP Certification
Having simple admittance to the adornments put away in your infrequent gems box is significant on the grounds that the gems you keep out of your sight normally get overlooked. Festival Jewellery
ReplyDeleteVery informative post ! There is a lot of information here that can help any business get started with a successful social networking campaign !
ReplyDeleteBest Institute for Data Science in Hyderabad
Clients marketing strategies that you choose to useful survey before establishing. It can be straightforward to jot down top-quality write-up like this. jewellery handmade
ReplyDeletePrettygalboho jewellery is made in Australia, and once you wear a ring that is Jewellery that is handmade you will never regret its uniqueness Jewellery has been around literally forever. Speaking of Jewellery forever, in ancient Egypt, where according to many the origin of wearing jewellery was started. Stretching back to 3000 – 5000 years back the jewellery was used to show the people how respectable and rich they were. In today's society we now are becoming more individual and wanting Unique Pieces that stand out and not 'ready made' or mass produced. Opals
ReplyDelete`
That is promotion deals ads for you to handy examine prior writing. It will be easier to write down better site like that. Beach Jewellery
ReplyDeleteThanks for the blog post buddy! Keep them coming... 木目金
ReplyDeleteWhile some people like authentic and expensive hand-crafted jewellery, others may simply want to stock their wardrobes with trendy and fashionable items. Honestly, both have their own pros and cons. Let's try and compare both types of jewellery on the basis of their quality, durability and affordability. Gems and Jewels
ReplyDeleteDue to this it is advisable that you have to relevant analysis previous to building. You may upload more practical upload by doing this. Tribal jewellery
ReplyDeleteI have wanted to write about something like this on my webpage and you gave me an idea. Cheers. Boho Earrings
ReplyDeleteI have wanted to write about something like this on my webpage and you gave me an idea. Cheers. Crystals
ReplyDeleteOur modern life is incomplete without FREE App Skype : Skype for Business
ReplyDeleteWe supply turn-key solutions for your specific diamond needs, from custom made designs to delivering exemplary diamond solutions. fancy cut diamond suppliers
ReplyDeleteGood website! I truly love how it is easy on my eyes it is. I am wondering how I might be notified whenever a new post has been made. I have subscribed to your RSS which may do the trick? Have a great day! friendship jewellery
ReplyDeleteNice post, getting FULL Information at one place its really good,, !!! Planet most love music app mp3 juice get here thanks ....
ReplyDeleteNice post, getting FULL Information at one place its really good,, !!! World most Famous app to make life easier without any problems thanks ....
Such sites are important because they provide a large dose of useful information ... Black satta king
ReplyDelete47FEFF7C4F
ReplyDeleteTakipçi Satın Al
Brawl Stars Elmas Hilesi
Vodka Fiyatları